Complete Activity Tracking
Real-time security and activity monitoring for your organization. Track authentication events, data access, and system activities with complete audit trails.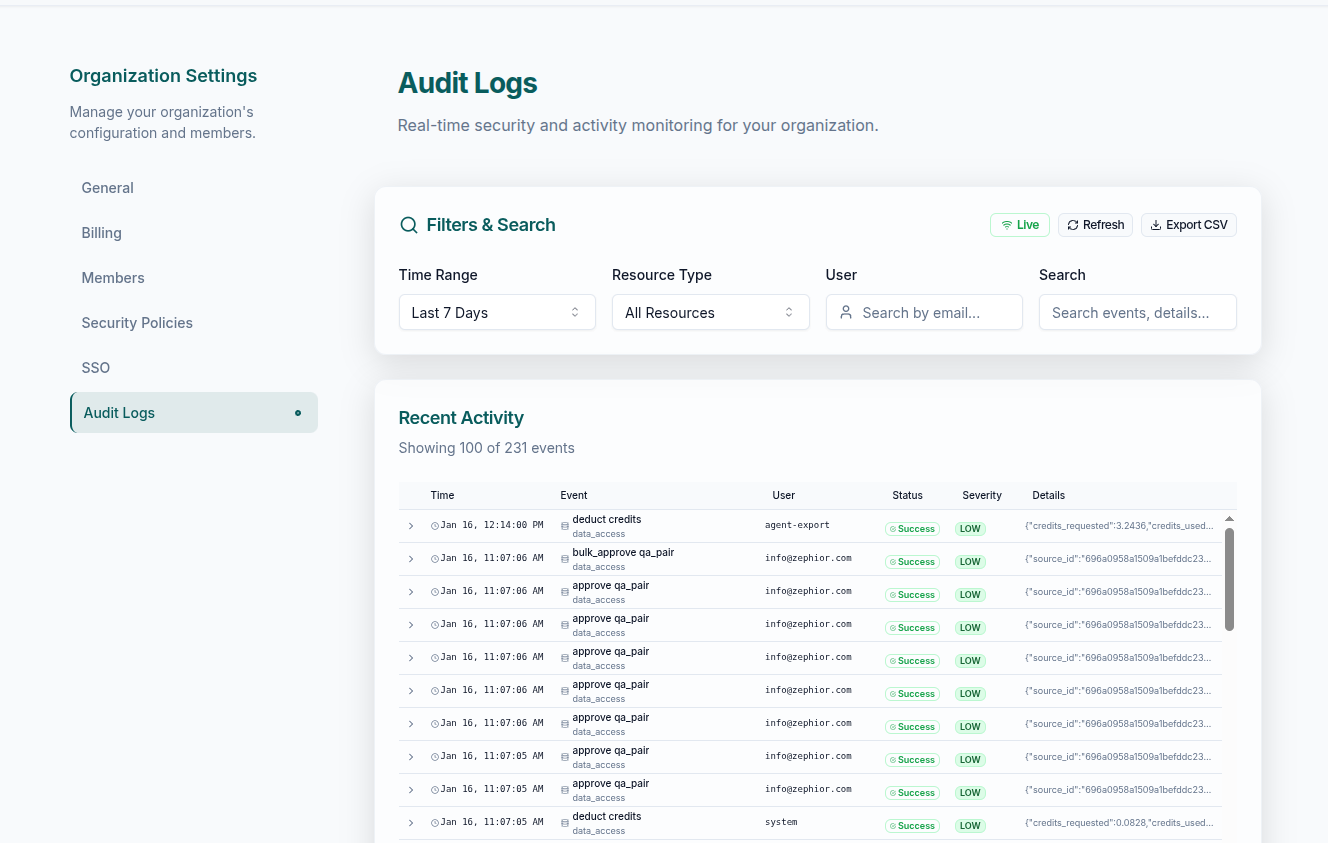
Real-Time Streaming
Live audit events streamed to admin users via WebSocket
90-Day Retention
Audit logs automatically retained for 90 days
CSV Export
Export logs for any time frame for compliance and analysis
Detailed Event View
Click any row for full event details including raw JSON
Event Types
- Authentication
- Data Access
- Security
- System
| Event | Description |
|---|---|
| User login | Successful sign-in with method and IP |
| Failed login | Incorrect credentials or blocked attempt |
| MFA verification | Multi-factor authentication challenge |
| SSO authentication | Single sign-on via identity provider |
| Logout | User-initiated session end |
Filtering & Search
Time Range
Last 24h, 7 days, 30 days, 90 days, or a custom date range
Event Filters
Filter by event type, severity, or resource type
User Search
Find all activity by a specific user
Severity Levels
| Level | Meaning |
|---|---|
| Info | Normal operations — logins, reads, routine actions |
| Warning | Unusual but non-critical — failed logins, permission edge cases |
| Error | Something went wrong — failed operations, system errors |
| Critical | Requires attention — access breaches, data integrity issues |
Event Details
Click any log row to expand the full event record:| Field | What it shows |
|---|---|
| Timestamp | Exact time of the event |
| Event Type | Category and specific action |
| User | Who performed the action |
| Resource | What was affected (source, file, QA pair) |
| Request Info | IP address, user agent |
| Full JSON | Complete raw event data |
Export
Export audit logs as CSV for compliance documentation, security audits, or external analysis.Exports are rate-limited to 10 per 24 hours per organization. Each export includes all event types for the selected time range.
Data Security
Sensitive data protection
Sensitive data protection
Audit logs automatically sanitize sensitive information before storage. JWT tokens, API keys, and passwords are redacted. Personal data is protected in compliance with GDPR and FADP.
Isolated storage
Isolated storage
Logs are stored in your organization’s own isolated database — the same security controls that protect your other data. All storage is in European data centers.
Request correlation
Request correlation
Every request is tagged with a UUID for end-to-end tracing. Connect related events across operations for debugging and compliance investigations.
Access Control
Compliance Use Cases
Security audits
Security audits
Export logs for external security auditors to demonstrate access controls and monitoring capabilities.
Incident investigation
Incident investigation
Use detailed logs to investigate security incidents, track unauthorized access attempts, and understand the scope of any issues.
User activity reports
User activity reports
Generate reports on user activity for internal reviews, identifying usage patterns and potential policy violations.
Compliance documentation
Compliance documentation
Maintain evidence of security controls for GDPR, SOC 2, and other compliance frameworks.
Related
Security Settings
Configure MFA, SSO, and password policies
Roles & Permissions
Manage roles and access levels
Team Management
Invite, remove, and manage members